Introduction
This article explores how StealthMole—a deep and dark web intelligence platform—can be leveraged to profile cybercrime activity across Latin America. By tapping into modules such as Ransomware Monitoring (RM), Leaked Monitoring (LM), Government Monitoring (GM), and Compromised Data Set (CDS), we uncover threat actor behavior, sector-specific targeting, and evolving threat patterns within the region.
Our analysis focuses on seven of the most targeted countries in Latin America: Brazil, Mexico, Colombia, Argentina, Chile, Peru, and Ecuador—all of which are heavily impacted by database breaches, ransomware attacks, malware infections, and phishing campaigns.
Regional Threat Intelligence Highlights
- Brazil stands out as the most affected country in the region, recording:
- 74 ransomware incidents
- 115 database leaks
- 9 government-related dataset exposures
- Over 189,000 compromised data records
It is followed by Mexico, Peru, and Argentina in terms of overall attack volume and data compromise.
- From January to July 2025, there were:
- 192 ransomware attacks across the 7 countries analyzed
- 49 distinct ransomware groups involved
- After Brazil, the countries most impacted by ransomware include:
- Mexico, Argentina, Colombia, and Peru
- Top targeted sectors by ransomware operations:
- IT services
- Food industry
- Educational institutions
- Chemical manufacturing
- Most active ransomware groups in LATAM:
- Akira
- Safepay (with a rising trend)
- Lockbit (showing a decline)
- Arcus Media
- Despite the law enforcement takedown of BreachForums in July 2025, threat activity has continued to escalate:
- 254 database leaks were observed between January–July 2025
- Leaks increased from 21 in June to 35 in July
- A small set of recurring actors were linked to multiple data breaches posted on cybercrime forums
- Government-related dataset exposures also remain a concern:
- 30 leaks involving government data were identified in 6 of the 7 countries during the same period
- These incidents continued to rise in July, even after BreachForums was taken offline
These insights reveal regional threat actor overlap, repeated targeting of specific industries, and cross-border links in malicious activity—critical for prioritizing intelligence targets and launching coordinated investigations across Latin America.
Ransomware Group Profiling via StealthMole
Our ransomware analysis for the 7 selected LATAM countries highlights the top 15 most active ransomware groups by number of attacks between January and July 2025. The data shows:
- 192 confirmed ransomware incidents
- 49 unique ransomware groups involved
- Group activity varies across countries and sectors, reinforcing the need for localized yet connected threat assessments.




The Safepay ransomware group has shown a notable rise in activity across the LATAM region, emerging as one of the most persistent and growing threats during the first half of 2025. Since its emergence in November 2024, Safepay has claimed 274 victims across multiple jurisdictions, including several high-profile incidents in Latin America.
Using StealthMole’s dark web monitoring capabilities, we were able to:
- Map Safepay’s onion infrastructure, including their leak and negotiation sites.
- Link a key operational email address—VanessaCooke94@protonmail.com—to one of their onion domains.
- Identify the same email address as being registered on both the US-based DigitalOcean cloud platform (via open-source intelligence from Osint.industries) and the US-based interserver.net hosting platform (via data from osint.lolarchiver.com).

Leaked Monitoring (LM) through StealthMole
Between January and July 2025, StealthMole’s Leaked Monitoring (LM) module recorded a total of 254 database leaks across the seven LATAM countries analyzed—Brazil, Mexico, Colombia, Argentina, Chile, Peru, and Ecuador.




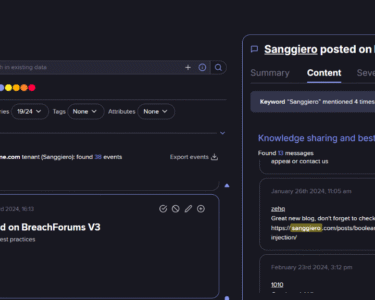
Case Study: injectioninferno & injectioninferno2
Between January and July 2025, the threat actor operating under the usernames injectioninferno and injectioninferno2 were linked to the sale of 27 distinct databases across multiple cybercrime platforms. The distribution of these leaks includes:
- 18 databases sold on breachforums.st
- 3 databases on breachforums.info
- 6 databases on darkforums.st
These leaked datasets predominantly targeted Brazil, Argentina, Peru, and Mexico, highlighting a broad geographic footprint across the LATAM region.
Further investigation through StealthMole’s monitoring capabilities revealed that the actor maintains a notable presence on Telegram, using the following user IDs:
- 7191752811 — linked to the handle @Injectioninferno (currently inactive)
- 5968788047 — linked to @Injectioninferno2 (active account)
By mapping the inactive Telegram user ID (7191752811), StealthMole enabled the identification of additional contextual information related to @Injectioninferno, creating valuable pivot points for deeper attribution and intelligence gathering.


In addition, the threat actor was identified as the administrator of the Telegram channel “Leads and Leaks” (@leadsandleaks1; ID: 2443211983), where various samples of leaked datasets are regularly posted. Further investigation into this channel was not pursued beyond this point.
Blockchain analysis has uncovered Bitcoin, Ethereum, and Litecoin addresses connected to this threat actor. Further investigation has linked Binance, Bitso, and Lemon.me cryptocurrency accounts to this individual.
Government Monitoring (GM) through StealthMole
Between January and July 2025, StealthMole’s Government Monitoring (GM) module detected 30 government-related database leaks across the LATAM countries analyzed. These leaks involved sensitive public sector data, posing significant risks to national security, citizen privacy, and governmental operations.
A detailed breakdown of government-related leaks by country is provided below.




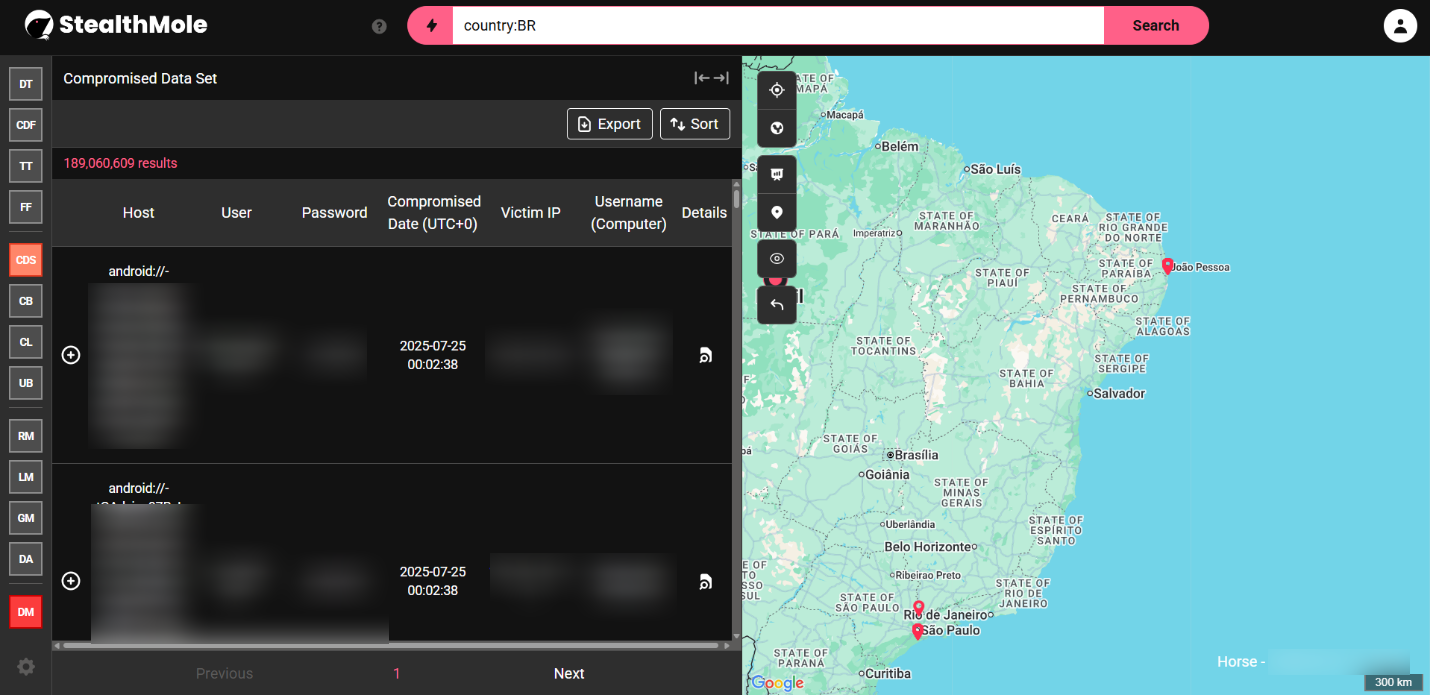
Compromised Data Set (CDS) Analysis through StealthMole

This module detects and attributes leaked credential dumps, email-password pairs, and sensitive data records associated with organizations or citizens from specific countries. A summary chart of the compromised data set (CDS) exposure by country is provided below.

Brazil – #1 Most Targeted
- Primary Threats: Phishing, banking malware (e.g., Grandoreiro), ransomware, and credential harvesting.
- Key Factors:
- Large digital banking sector and widespread mobile usage.
- High number of local threat actors and malware families originating in Brazil.
- Frequent use of Telegram and WhatsApp in cybercriminal operations.
Mexico
- Primary Threats: Business email compromise (BEC), ransomware (LockBit, Cl0p), and data breaches.
- Key Factors:
- High concentration of multinational companies and government targets.
- Often used as a gateway to attack U.S.-linked supply chains.
- Vulnerable public infrastructure and poorly secured systems in SMEs.
Colombia
- Primary Threats: Ransomware, phishing, and attacks on critical infrastructure.
- Key Factors:
- Government institutions and the financial sector are frequent targets.
- Ongoing digitization efforts increase attack surface.
- Criminal groups using cyber tactics alongside physical crime.
Argentina
- Primary Threats: Insider threats, ransomware (e.g., LockBit, Akira), and DDoS attacks.
- Key Factors:
- Growing IT sector with inadequate cybersecurity investment.
- Recurrent attacks on government portals and public services.
- Rise in hacktivist activity during political unrest.
Chile
- Primary Threats: Ransomware, website defacements, data theft.
- Key Factors:
- Advanced digital transformation in finance and healthcare sectors.
- Several large-scale breaches of national government institutions in 2023–2024.
Peru
- Primary Threats: Phishing, ransomware (e.g., LockBit), government data leaks.
- Key Factors:
- Surge in phishing attacks places Peru among the top 3 most targeted in LATAM.
- Repeated ransomware incidents affecting public institutions and tax platforms.
- Limited cyber maturity in public infrastructure despite increased digitization.
Ecuador
- Primary Threats: Ransomware (e.g., LockBit), malware, critical service disruption.
- Key Factors:
- Attacks on municipal systems, intelligence services, and major banks.
- Ranked low on global cybersecurity readiness (ITU GCI).
- Gradual improvements through national cybersecurity policy launched in 2023.
Conclusion: The Strategic Importance of Regional Cybercrime Monitoring in LATAM
The findings presented throughout this analysis demonstrate the role of regional cybercrime monitoring and dark web intelligence in addressing the escalating threat landscape across Latin America. By leveraging StealthMole’s integrated modules—including Ransomware Monitoring (RM), Leaked Monitoring (LM), Government Monitoring (GM), and Compromised Data Set (CDS)—organizations and national CERTs gain the ability to detect, track, and respond to threat actors operating at scale across borders.
Several key patterns emerged through this investigation:
- Repeat actors such as injectioninferno and Safepay ransomware group have been found targeting multiple LATAM countries.
- Threat activity is increasingly converging across platforms, with actors operating on traditional forums, and Telegram groups and channels simultaneously.
- Government and citizen data are being commoditized at alarming rates, with ongoing database leaks even after major forum disruptions like the takedown of BreachForums[.]st.
- The geographic overlap of compromised datasets, ransomware activity, and actor presence supports the case for cross-border cooperation and intelligence fusion.
StealthMole’s ability to correlate threat actor identities, infrastructure, language use, leak patterns, and forum activity across jurisdictions makes it an invaluable platform for:
- Uncovering regional threat ecosystems
- Identifying shared adversaries targeting multiple LATAM countries
- Supporting collaborative investigations between governments, CERTs, and the private sector
- Enabling proactive defense through timely visibility into emerging threats
In a region where cybercriminal activity is rapidly evolving and becoming increasingly interconnected, continuous intelligence collection and coordinated analysis are essential.
StealthMole enables this at scale.