A Polish crypto scammer has stolen over $2M since 2022 using a mix of social engineering, fake identities, and wallet-draining tactics.
- Modus Operandi: Pretends to be a confused crypto beginner with a gambling problem, offering 20–50 SOL upfront to victims for help setting up wallets. During live calls (Discord, Zoom, Telegram), he tricks them into exposing credentials or granting remote access, then instantly drains their wallets.
- Aliases: Operates under multiple names including Filip Weiner, Igor Werner, Darek Velten, Gregor Wersen, and Vlad Cervantes.
- Platforms Abused: Discord, Telegram, X.com, Twitch, Zoom, and crypto betting sites such as Shuffle.com.
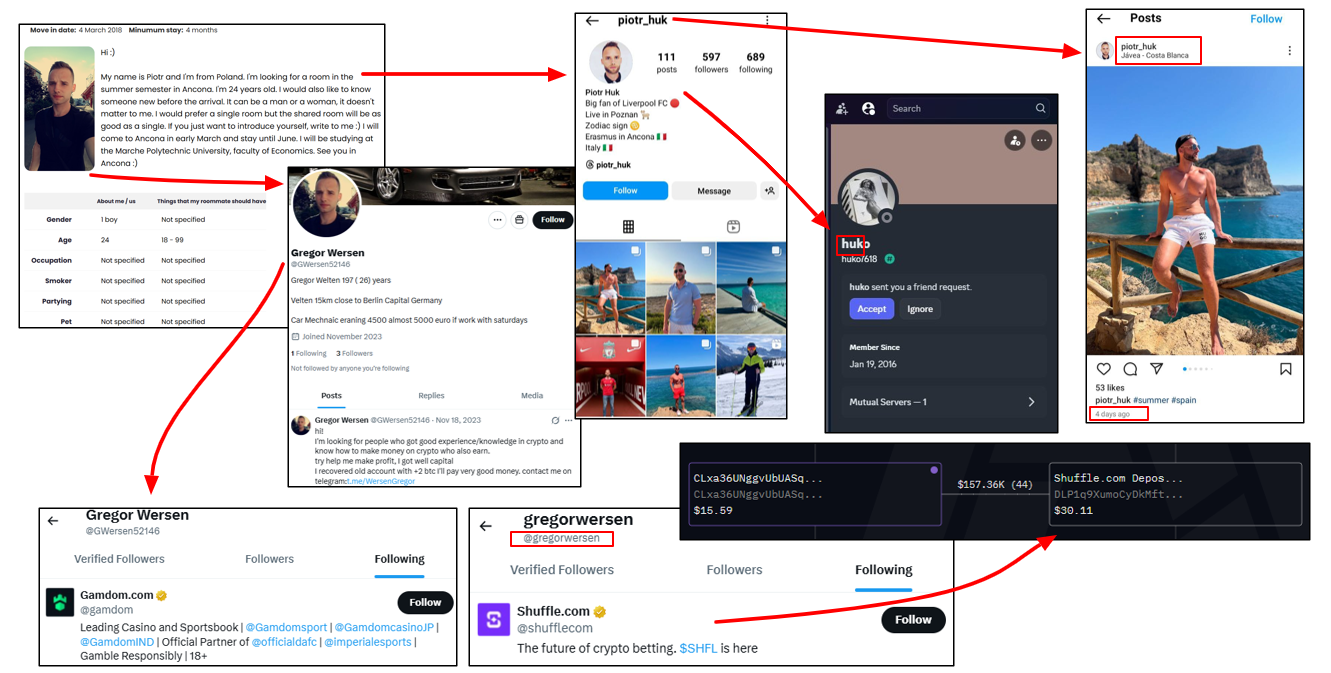
- OSINT Findings: Dozens of linked accounts were uncovered. Disposable phone numbers in Poland, Germany, and Turkey were tied to the fake personas. Reverse image searches and social media traces connect the scammer to a Polish national named Piotr Huk, aged 32, based in Poznań.
- Crypto Analysis: On-chain investigation reveals three main Solana addresses handling over $3.9M in inflows. Funds were funneled to Shuffle.com, Binance, Bybit, Circle.com, and KuCoin. Some wallets maintain direct links to igortrading.sol, strongly tying the aliases together.
- Red Flags for Investigators:
- Victims lured with upfront payments or job offers
- Requests for screen sharing or remote access
- Frequent switching between aliases and platforms
This case highlights how OSINT + blockchain forensics can expose elaborate scammer personas, link disposable identities, and trace illicit funds across multiple platforms.

The suspect is a skilled social engineer who has perfected the art of manipulating victims during live interactions. His typical method involves asking someone to show him how to set up an Axiom wallet via Discord screen sharing. To gain trust, he even pays 20–50 SOL upfront.
His psychological manipulation is striking: he pretends to be confused, feigns fear of being hacked, and insists that the victim take extra precautions so that he cannot see their sensitive information.
Despite this performance, while the victim is screen sharing, he captures the Axiom wallet password. Once the victim connects a trading wallet, he drains it instantly.
Operating under multiple Discord, X, and Telegram aliases, this individual has drained numerous Solana wallets in recent weeks. His criminal activities date back to at least 2022, with over $2M+ stolen to date.
His typical persona is that of a crypto newbie with a gambling problem. He builds trust, then tricks victims into granting remote access through Zoom, Discord, or Telegram. Known aliases include:
- Filip Weiner
- Igor Werner
- Darek Velten
- Gregor Wersen
- Vlad Cervantes
Observed Tactics
- Offers free Solana or small payments (e.g., 5 SOL) to “learn trading”
- Uses Zoom/Discord to obtain remote access
- Installs malware or directly transfers funds
- Use fake personas to build credibility
- Targets crypto professionals with fake job offers or investment pitches
OPSEC Model: Tracking the Fake Accounts
Through analysis of X.com posts and reports by researchers and victims, multiple linked accounts were uncovered across platforms.
| Platform | Username / ID | Notable Details |
| Discord | gregormayer | Not identified; inactive |
| Telegram | GregormayerDE | Not identified; inactive Linked Phone number: +49-15781447867 |
| Discord | Huko7618 | Not identified; inactive Registered: 19 January 2016 |
| Telegram | Filipweiner97 / 8007727943 | Name: Filip Weiner – Active |
| X.com | filipweiner | Not identified; inactive Name: Filip Weiner |
| Twitch | filipweiner1997 / filipweiner | Name: Filip Weiner – Active |
| Discord | filipweiner1997 | Not identified; inactive |
| Telegram | iwerner97 / 7226305834 | Active; member of @MoriChatEng ($MORI COIN ENG CHAT) |
| Telegram | Iwerner1997 / 7223007824 | Active |
| X.com | IWerner1997 | Not identified; inactive |
| Telegram | darekvelten | Not identified; inactive |
| Telegram | webpander | Not identified; inactive Name: Igi I Linked Phone number: +90-5369383042 (Turkey; Turkcell) |
| Telegram | gregorwersen | Not identified; inactive |
| X.com | GWersen88745 / 1750850324959809536 | Name: Gregor Wersen – Active Registered: January 2024 Registered Email: gr****************@gmail.com |
| X.com | GWersen52146 / 1725940753451401216 | Name: Gregor Wersen – Active Registered: November 2023 Bio: Gregor Welten 197 ( 26) years Velten 15km close to Berlin Capital Germany Car Mechnaic eraning 4500 almost 5000 euro if work with Saturdays Linked Telegram: WersenGregor (Inactive) Following: Gamdom.com (online casino) |
| X.com | Gregorwersen / 1800210404045369344 | Registered: June 2024 Following: Shuffle.com (crypto betting platform) Active |
| X.com | GregorWersen97 / 1706058216885669888 | Registered: September 2023 Active |
| YouTube | Gregorwersen / UCR1lR_O3d4P1GvwWvfxhIDw | Registered: 6 May 2024 Short Bio: Gregorwersen 97 (27) years Berlin’s mechanic maestro in Velten. 2 subscribers Active |
| Steam | gregor97wersen / 76561199572148653 | Name: Gregor Wersen – Active |
| GitHub | GregorWersen / 140273857 | Registered: 22 July 2023 Active |
| Twitch | Gregorwersen / 1223664258 | Active |
| Twitch | gwersen1997 / 1239852398 | Active |
| Discord | gwersen1997 | Not identified; inactive |
| Gregorwersen / 66188807294 | Name: Gregor Wersen – Active Registered: May 2024 Registered Email: *@hotmail.com | |
| Gregor_0_3 / 60851432613 | Name: Gregor Wersen – Active Bio: July 2023 Bio: 25, Berlin | |
| Gregorwersen8 / 66373516968 | Name: Gregor Wersen – Active Registered: May 2024 Bio: Car enthusiast, 27, Velten, Germany | |
| ID: 122102453006449481 | Name: Gregor Wersen – Active Claimed Location: Velten, Germany |
Chat Intelligence: Telegram Activity
User iwerner97 (ID: 7226305834) → low activity overall, but on 29 June 2025 was identified attempting to acquire $MORI coins in @MoriChatEng.

- On 22 Feb 2025, posted about social engineering scams in @solanamoneyglitch.
- In the same group, sought partners for a memecoin trading project.

| Linked Fake Name | Phone Number | Notable Details |
| Gregor Wersen | +48-459078293 (mobile; Poland; Mobiledata Sp. z o.o.) | Registered on Wise under the name “Amina Merdaci”; on Zepeto (“mx2jlou”) |
| Filip Werner | +48-782076129 (mobile; Poland; Polkomtel Sp. z o.o. – Plus) | Linked to @Filipweiner97 on Telegram |
| Igor Werner | +48-695872471 (mobile; Poland; Polkomtel Sp. z o.o. – Plus) | Linked to @iwerner97 on Telegram; registered on OK.ru (ID: 910177156457) and Facebook |
| Gregor Mayer | +49-15781447867 (mobile; Germany; Telefonica Germany GmbH & Co. OHG) | Linked to GregormayerDE on Telegram Registered on Facebook, WhatsApp |
OSINT 4 Good: Behind the Fake Personas
A reverse image search of the “Gregor Wersen” profile photo revealed it belonged to Piotr, a Polish national. On 4 March 2018, Piotr posted on erasmusu.com while seeking accommodation in Ancona, Italy as part of an Erasmus scholarship.

- Instagram: piotr_huk (since March 2014) → Liverpool fan, lives in Poznań, travels frequently (noted in Javea, Spain, 15th Aug 2025). Born June 1993 in Ostrów Wielkopolski (age 32).
- Education: Studied at Marche Polytechnic University, Faculty of Economics.
- Facebook: Last active Feb 2024 (ski trip in the Alps). Family in Poland.
- LinkedIn: Senior Business Analyst at ADM (pet and animal nutrition company) since March 2023.
- Connection: The alias “Huko7618” (used in Discord campaigns) matches his surname “Huk”.
Crypto Analysis: On-Chain Insights
The following crypto addresses were reported as linked to the scammer:
| Crypto Address | Notable Details |
| 76iXe9yKFDjGv3HicUVVy8AYxHLC71L1wYa12zaZzHHp | Shuffle.com account |
| CLxa36UNggvUbUASqinuHxUFtXXoEx3UoHKKEEGEdL2j | Incoming and outgoing transactions to Shuffle.com; outgoing transactions to a Binance account |
| 7epx39b8g3rbkYaoTnb5NaaW1AC3CDEqevySNkrzJHGw | Incoming and outgoing transactions to igortrading.sol; outgoing transactions to a KuCoin deposit address |
| 0x2bd923b4496c779B67B957131e1f8fb4e56F1220 | ~$19 received |
| AvLhqqnDk8QTwKFeYR9epTBTTEgEurQVwXjcemuAEeEW | Deposit for igortrading.sol; outgoing transactions conducted with a Bybit deposit address, a Shuffle.com deposit address, Circle.com addresses |
- Scammer’s SOL Address I: CLxa36UNggvUbUAS[…]
- Received $1.4M+ total.
- Withdrawals: ~$160K → Shuffle.com, ~$4K → Binance, ~$100 → Gamdom.com.
A transaction flowchart for Scammer’s SOL Address I is provided below via Arkham Intelligence.
- Scammer’s SOL Address II: 7epx39b8g3rbkYao[…]
- Received $1.2M+ total.
- Withdrawals: ~$23K → KuCoin, ~$63K → Jupiter, unlabelled 6ga7g32Qrm (later → Bybit.com).
- Strong link with igortrading.sol.
A transaction flowchart for Scammer’s SOL Address II is provided below via Arkham Intelligence.
- Scammer’s SOL Address III: igortrading.sol [AvLhqqnDk8QT]
- Received $1.3M+ stolen assets.
- Transactions: with Pump.fun account [4gde58vrD96u], Bybit, Shuffle.com, Circle.com.
- On 10 July 2025, transferred stolen funds to DjNvLj85ZVLv → Binance wallet (potential subpoena target).
- Cross-linked with Scammer’s SOL Address II (~$23K).
A transaction flowchart for Scammer’s SOL Address III is provided below via Arkham Intelligence.

This case underscores how well-crafted social engineering combined with multi-platform identity hopping can still evade casual detection. Investigators, researchers, and crypto professionals can take the following steps to mitigate risk and strengthen attribution:
- For Investigators & Researchers
- Use OSINT platforms such as Osint.industries, osint.lolarchiver.com, and Arkham Intelligence to cross-reference fake profiles, identify linked assets, and map transaction flows.
- Apply AMLBot and other blockchain compliance tools to assess counterparties, monitor risky addresses, and trace stolen funds through exchanges and mixers.
- Correlate disposable phone numbers, usernames, and images across platforms to uncover real-world links.
- Preserve screenshots and chat logs as evidence — scammers frequently delete or rebrand their accounts.
- For Crypto Professionals & Victims
- Never share screens or allow remote access when handling wallets.
- Treat offers of “free crypto” or upfront SOL payments as red flags.
- Use hardware wallets and secure password managers to minimize exposure.
- Report suspicious activity and wallet addresses to exchanges and platforms for blacklisting.
Disclaimer
This is an ongoing investigation. The information presented here reflects findings available at the time of publication. Further evidence, linked accounts, or transaction details may surface in the future, which could refine or expand upon the conclusions outlined in this brief report.