We’re launching a new Cyber Threat & Trend Tracker, providing concise, intelligence-led summaries of the latest threat actor tools, panels, and infrastructure we’ve observed across Telegram and dark web platforms. This ongoing series will support investigators, researchers, and stakeholders with timely updates. For deeper insight or attribution support, detailed investigation packages are available upon request.
🧰 Crypto Draining, Phishing & Social Engineering Toolkits
- Bratva Coinbase Panel – Detected on Telegram
- Found in group “NFT/Crypto Drainers | Group chat” (@draincryptoez; ID: 2560073302)
- Advertised in both Russian and English
- Owner: @GOATXMR (ID: 7365647296; prev. @apoortel; former display: “Molli СС”)
- Group created: 22 May (84 subs as of 3 August)
- Channel: @bratvacbpanel (ID: 2669432154; 8 subs)
- Bot: @Bcbpanelbot (ID: 7160455865)
- Price: $2,100; accepts BTC and LTC
- Additional wallets linked: Tron and Ethereum
- Attribution: Off/On-chain intelligence suggests Chinese origin
📸 Supporting Screenshots
- OXF PANEL – Detected on Telegram
- Used in phishing/social engineering campaigns
- Telegram group “OXF ADVANCED PANEL” created 30 May (362 subs)
- Owner: @oxf_admin (ID: 7838371363)
📸 Supporting Screenshots
- Angel Mailer – Detected on Telegram
- Phishing tool with email templates for Coinbase, Binance, Gemini, Nexo, Apple, Ledger, Kraken & more
- Price: $2,000 + 10% fee (full mailer access)
- Telegram channel: “Angel AIO” (108 subs)
- Owner: @angelmailersupport (ID: 7972848879)
📸 Supporting Screenshots
- Spectre Panel (Advanced Coinbase Dashboard) – Detected on Telegram
- Used in crypto phishing attacks
- Price: $1,750 (full source code; middleman optional)
- Channel: @SpectrePanel (ID: 2635571150; 47 subs)
- Owner: @equalizer1337 (ID: 7556475877)
📸 Supporting Screenshots
- RedLock Press One (RedLock P1) – Detected on Telegram
- Social engineering toolkit with 500 concurrent call support
- Pre-recorded audio for Coinbase & Kraken
- Price: $2,000 access fee
- Channel: @RedLockP1 (ID: 2367917229; 7,000+ subs)
- Owner: @RedLockSupp (ID: 8198684244; prev. @omw2nyc)
📸 Supporting Screenshots
- GokuSkyBase Redirect Link – Detected on Telegram
- Offers Coinbase phishing toolkit and multi-drainer panels
- Channel: @skypanels (ID: 2798147649; 76 subs; created 8 June)
- Price: $750 (source code included)
- Linked Channel: @gokuskybaseredirect (ID: 2383066107; 10 subs)
- Owner: @gokumbire (ID: 7916920721)
📸 Supporting Screenshots
- Katana Drainer Kit – Detected on Telegram
- Web3 phishing kit, supporting 60+ chains (ETH, TRON, COSMOS, SUI, MATIC, SOL, AVAX etc.)
- Advertised in Russian and English
- Channel: @KatanaKitUpdate (ID: 2803556262; 423 subs; created 13 July)
- Bot: @KatanaDrainer_bot (ID: 8282470400)
- Owner: @katana_dev (ID: 8021795593)
📸 Supporting Screenshots

- Malware GPT – Detected on Telegram
- Custom uncensored AI platform designed for red teamers and malware devs
- Channel: @OfficialMalwareGPT (ID: 2715877106; created 16 July; 75 subs)
- Owner: @MalwareGPTSupport (ID: 8143956278)
- Linked to: @CellikRat_New (ID: 2602759132), vendor on Hackforums
📸 Supporting Screenshots
- ObscurGPT – Detected on Telegram
- Used for scripting crypto drainers
- Bot: @ObscurGPT_bot (ID: 7881522472); detected 28 July
- Channel: @ObscurGPT (ID: 2626459988; 34K subs)
- Website: ObscurGPT[.]com (hosted by Hostinger)
- Owner: @KGAMI5 (ID: 991047960; French)
📸 Supporting Screenshots

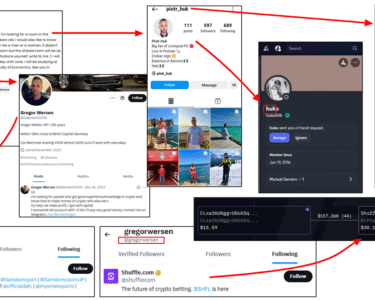
- LumiStealer (Discord infostealer) – Detected on Telegram
- Group: “LumiStealer” (ID: 2725408466; 5 members; created 17 May)
- Owner: @macanxp (ID: 5873642590); Intelligence suggests Brazilian origin
- Username “Macanxp” identified on TikTok (geolocation: Brazil), Twitch, X.com, Instagram (data sourced via osint.industries)
- SHA-256: c9d8c91666f3b7c1c1e4c3f1ebfef5a26d6c7cbcbed21d70dcd830cf718f4518
- 0 detections on VirusTotal
- Copyright: © 2025 Thief Developers
- Certificate Signer name: “RAFAEL RIBEIRO GONÇALVES”
- YouTube demo: youtube.com/watch?v=eQSA9AkIGVg; linked Telegram group @loaderxp (ID: 2764279949; created on 20 June 2025)
📸 Supporting Screenshots (data sourced via Virustotal.com)
- GenesisStealer (Discord infostealer) – Detected on Telegram and Discord
- Telegram Channel: “@AdsGenesis0” (ID: 2812444524; 30 subs; created on 15 July)
- Telegram Group: @GenesisStealer (ID: 2298242613; 226 members)
- Telegram Owner: @zitrax77 (ID: 5748136272); Seller @wbvt6 (ID: 6025702345)
- Discord Server: 1348514347084677174
- Discord Owner: zitrax (ID: 1354138218198732890)
- Telegram account @zitrax77 and PayPal account @zitrax77 indicate the individual’s name to be Amir Zitrax (French origin)
📸 Supporting Screenshots
- EvilSoul (Discord infostealer) – Detected on Telegram
- Telegram Group: @EvilSoulStealer (ID: 2560038563; 206 members)
- Telegram Owner: @breakingupslow (ID: 5834325304); Intelligence suggests Brazilian origin
- Username @breakingupslow identified on Roblox (ID: 8773549615)
📸 Supporting Screenshots

- noTrace – One-way to Privacy – Detected on Telegram
- Channel: “noTrace – One-way to privacy” (873 subs; created 17 May)
- XMR-based crypto exchange; supports swaps with LTC, ETH, USDC, BTC, DAI, XRP, etc.
- No KYC required
- Owner: @notracesup (ID: 102041533)
- Bot: @notraceexchbot (ID: 7985676636)
📸 Supporting Screenshots

- RDP Express – Detected on Telegram
- Channel: @rdp_express (ID: 2707250472; 566 subs; created 17 July)
- Offers US-based RDP & VPS services
- Owner: @rdpexpress (ID: 8177032221)
📸 Supporting Screenshots
- QWINS LTD – Detected via Cyber Intelligence Insights Substack
- UK-incorporated, Russian-run hosting provider (AS213702; qwins[.]co)
- Hosting various malware (Amadey, Lumma, Vidar)
- VPS starting at $2/month
- Transactions traced to Heleket.com (non-KYC exchange); Received $7,500+ in their ETH wallet.
- Heleket operated by Handy Group LLC (Reg. 406214902, Tbilisi, Georgia)
- Growing trend: bulletproof providers migrating to Heleket
📸 Supporting Screenshots (data sourced through AMLBot)
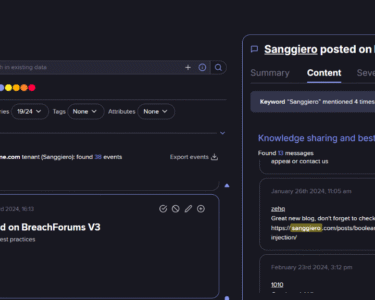
- VMHeaven[.]io – Detected via Dark Web Informer (8 August)
- Domain: Vmheaven[.]io (registered 12 December 2024; updated 15 February 2025)
- Hosting: IP subnet 45.156.87.0/24 (Pfcloud UG – AS51396; Aachen, Germany)
- Activity: Hosting Coinbase phishing panels (e.g., 143221-cb[.]com)
- Profiles:
- X.com: @vmheaven (email: se****************@duck.com)
- GitHub: @vmheaven (email: lake-engorge-trade@duck.com)
- Forums: @vmheaven (Patched[.]to, Cracked[.]sh, Hackforums[.]net, Oguser[.]com)
- Discord: ID 894332418662752257; Server ID 1318705521317904474
- Email lake-engorge-trade@duck.com registered on OVH.com cloud platform (via osint.lolarchiver.com)
- Telegram: @vmheavenlinks (ID: 2745560439; 50 subs; created 22 June)
- Telegram Owner: @VMHeavenAdmin (ID: 187125216; Arabic language)
- Crypto: Payment provider Plisio[.]net; Bitcoin cluster tagged via AMLBot
📸 Supporting Screenshots

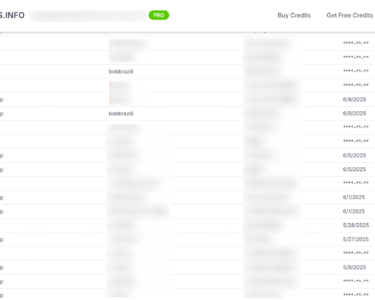
- BEAST – Detected via Dark Web Informer (29 July)
- Claimed 16 victims
- Platform: TOR
- Email addresses identified and mapped via StealthMole
- Backend IPs:
- 89.248.163.12 (IP Volume Inc)
- 185.193.88.44 (Telkom Internet LTD)
- Both hosted in Amsterdam, Netherlands
📸 Supporting Screenshots (data sourced via StealthMole)
- Blacknevas – Detected via Dark Web Informer (6 August)
- Claimed Victims: 12 (Technology – 2; Business Services – 2; Energy – 1; Hospitality & Tourism – 1; Consumer Services – 1; Manufacturing – 1; Education – 1)
- Platform: TOR
- Backend IP: 185.157.215.217 (hostname: v287054.hosted-by-vdsina.com; SERVERS TECH FZCO (AS216071), Amsterdam, Netherlands
- Etag: “683eeede-1c4”
- Technical Indicator: Favicon icon/hash mm3 -1207029254 matches INC Ransom onion site (incblog6qu…[.]onion) – suggests possible rebranding, impersonation, or affiliate activity
- INC Ransom Background: Active since at least July 2023
- INC Ransom Primary Targets: Healthcare, education, manufacturing, construction, and professional services – focus on SMBs, but includes some large enterprises
- INC Ransom Total Claimed Victims: 407
📸 Supporting Screenshots (data sourced via Shodan.io)