Introduction to Flare
Flare is a threat intelligence platform that consolidates monitoring across thousands of cybercrime forums and clear web sources. It enables proactive detection of threats before they escalate into full-scale cyberattacks. Among its key capabilities are:
- Telegram monitoring
- Ransomware leak tracking
- Threat flow explorer and intelligence
- Leaked credential detection
- Stealer log analysis
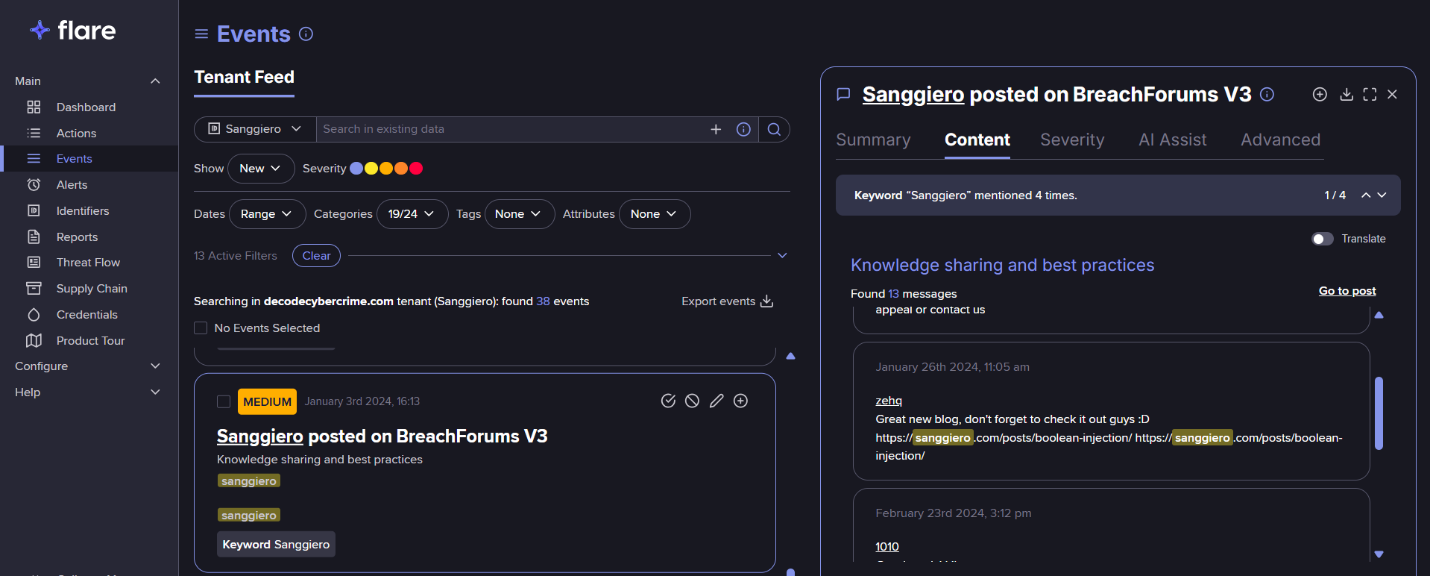
Investigative Insights: Sanggiero’s Digital Footprint
Using Flare’s intelligence tools, we tracked the online activity of the user known as Sanggiero (Telegram ID: 5879429917), who has been active across BreachForums and Telegram. Flare’s historical data shows that this individual has ties to the cyberattack targeting Acuity Inc, a U.S. government contractor. The attack appears to have involved collaboration with known threat actors EnergyWeaponUser and IntelBroker.
In February, IntelBroker—revealed by the U.S. Department of Justice as Kai West, a 25-year-old individual—was arrested and charged with causing over $25 million in damages. In June, four additional suspects affiliated with Breachforums—ShinyHunters, Hollow, Noct, and Depressed—were arrested in France. Notably, Sanggiero is not officially listed among the indicted individuals, and no conclusive link has been established between Sanggiero and any of the aliases involved in the arrests.
Some members of the BreachForums community have speculated that Sanggiero may have also operated under the moniker Noct, but our investigation has not found definitive evidence to support this claim.
Attributed Cyber Activity
Sanggiero has been associated with multiple alleged breaches and data leaks, including:
- Robert Half (U.S. recruitment firm – in association with IntelBroker)
- Tech in Asia (technology news outlet)
- HSBC and Barclays (in connection with IntelBroker)
- Halara (Hong Kong-based athleisure brand)
- PandaBuy (e-commerce platform – in association with IntelBroker)
- Mashvisor (U.S. real estate analytics firm – in association with IntelBroker)
Online Presence and Traces
Using Flare’s archival capabilities, we identified historical forum posts tied to Sanggiero on BreachForums. These posts reference a domain associated with the individual—sanggiero.com. A screenshot of the linked site is included below for documentation purposes.

Using Web.archive.org, we examined historical snapshots of sanggiero.com to gather additional information related to the website. The archived content provides insight into the user’s digital footprint and may reflect affiliations, interests, or infrastructure used to support cybercriminal activity.
Below is a screenshot of one of the archived versions of sanggiero.com, which serves as a reference point for ongoing analysis.

The screenshot above reveals that sanggiero.com publicly listed four cryptocurrency donation addresses. The table below summarizes the known financial activity tied to each address:
| Blockchain | Address | Total Received (USD) |
| Bitcoin | bc1q6see67av29kz6pm5tt24kcnrq3ytw0vatnlczf | $0.00 |
| Ethereum | 0x8411fDe0b30ea6dD16aE1815eef591E3A470A654 | $15.19 ($14.19 sent to Crypto.com) |
| USDT (TRC-20) | TK3Yinx79PpPkZR7r1ci1qMLTnw8JSZPiU | $0.00 |
| Litecoin | ltc1qjq6ww7p63kn0na5mqdtp2qja9r5l3ngazy0wkt | $9.05 (received from Kucoin.com) |
These addresses provide a minimal, yet traceable, on-chain footprint. The Ethereum and Litecoin addresses show limited but notable transactional activity, including interaction with Crypto.com and KuCoin.com—centralized exchanges that could serve as potential leads for further attribution if law enforcement subpoenas were pursued.
Blog Content Overview
On sanggiero.com, several blog articles authored by the user offer a glimpse into claimed intrusion techniques and operations. These posts outline a range of alleged cyberattacks and data breaches, primarily targeting U.S.-based organizations and platforms:
- “Hacking cloud of a US university” — 14 December 2023
- “Blind SQL which leaks 1M of data on an American sales website” — 13 November 2023
- “Infiltrating a critical multinational American infrastructure and stealing confidential documents” — 13 August 2023
- “Unauthorized access exploiting unvalidated JWT Tokens reveals 5M data” — 8 August 2023
- “How I was able to access millions of ID cards on an e-commerce platform” — 27 July 2023
Each post appears to describe successful exploitation techniques, data access, and at times exfiltration.
Self-Portrayal and Background Claims
In the blog’s About section, Sanggiero describes himself as having over 10 years of experience in cybersecurity, or as he phrases it, “into the world of computer vulnerabilities”.
Social Media Links
The sanggiero.com website listed multiple social media and communication platforms used by the individual. A summary of confirmed and associated accounts is provided below:
| Platform | Username / ID / Email | Notes |
| GitHub | Sanggiero | Inactive; currently active account is @sanggieuro |
| X.com (Twitter) | @sanggieroreal | Account suspended |
| Tutanota | sanggiero-sec@tutanota.com | Registered on GitHub, Docker, Namecheap |
Additional Potentially Associated Accounts
| Platform | Confidence | Username / ID / Email | Notes |
| YouTube | Low | @Sanggiero / UCzjjo3Tdi6eJAyLeeU6wBfA | Registered: 21 Sep 2018; Display name: Senator |
| Steam | Low | Sanggiero / 76561199185609701 | Display name: benz |
| Minecraft | Low | Sanggiero / 00a7c1bd28b84f8e93e77525aa600de5 | — |
| Matrix.org | Moderate | Sanggiero | Display name: IntelBrokers |
| Docker | Low | Sanggiero / 30d0b4c21c9c42959ce86b1c7b6074b9 | Registered: 29 Jul 2023 |
| Roblox | Low | Sanggiero / 8163541245 | Registered: 16 Mar 2025 |
| Telegram | Moderate | Sanggiero / 5879429917 | Display name: pandabuy fan club Email: sanggiero@xmpp.jp |
Corroborating Links and Artifacts
Further research linked the alias to additional accounts and development activity:
- GitHub account sanggieuro, confirmed through association with sanggiero.com.
- Email address sanggiero@cock.li, used to register:
- Dropbox account (display names: Vinny Troia; Abrielle Coppins)
- X.com account
- Ovh.com cloud platform account
- A notable GitHub repository titled “aws-federated-signin-url-generator” was linked to sanggieuro. The tool is a Flask-based Python application that generates AWS Management Console sign-in URLs using AWS STS federation tokens—a capability potentially useful for privilege escalation in cloud-based intrusion scenarios.
The Tutanota email sanggiero-sec@tutanota.com was also confirmed as the registration email for GitHub, Docker, Namecheap accounts.
Telegram Marketplace Activity
Through Flare’s monitoring of cybercrime communities, a Telegram channel—t.me/sanggieromarketplace (Channel ID: 1611389848) was identified in a BreachForums post dated 6 January 2024. The channel is described as the “Official marketplace for Sanggiero’s data & IntelBrokers”, and directly links back to sanggiero.com. As of this writing, the channel had 74 subscribers.
Breached Data for Sale on the Telegram Channel
The following datasets were advertised for sale via the channel:
- HopSkipDrive (US) – Personal documents including driver’s licenses, vehicle info, insurance, SSNs (~2000+), and selfies.
- Skybound Entertainment (US) – 180,000 user records with names, emails, partial credit card data, home addresses, and spending history.
- Sphero (US) – Over 1M user records including API keys, personal data, and avatars.
- ChowNow (US) – Source code repositories and internal project data.
- Sanmina (US) – Employee PII, internal documents, and credentials.
- Halara (US) – Customer data including full names, addresses, phone numbers, and region-specific identifiers.
- Perromart (Singapore) – Detailed user data with addresses and contact information.
- Renewbuy (India) – User records including passwords, contact info, and regional identifiers.
- Kameymall (China) – Latest breach advertised on 16 April 2024.
Expanding the Investigation Through Breach Data
Deeper analysis into historical breach records has revealed additional personally identifiable information (PII) and behavioral patterns associated with the alias Sanggiero, enabling the expansion of the digital profile.
Email Linkage to BreachForums and Network Metadata
The user Sanggiero was previously registered on breachforums.vc using the Gmail address:
tumetrouvesbeauoupas@gmail.com.
- Registration IP Address: 77.203.46.226
- Geolocation: Mulhouse, France
- ISP: Société Française du Radiotéléphone (SFR SA)
- Connection Type: Mobile Network
- Last Seen IP Address: 104.244.79.44
- Geolocation: Luxembourg
- ISP: FranTech Solutions
- VPN Provider: ProtonVPN
These IPs suggest the user may reside in or frequently connect from Mulhouse, France, and relies on privacy-enhancing services such as ProtonVPN for operational security (OPSEC).
Cross-Platform Exposure via OSINT Tools
Using platforms like Osint.industries and Epieos, we tracked the Gmail address across various services, uncovering further points of correlation:
| Platform | Username / ID | Notes |
| General Motors | N/A | No user details recovered |
| Corsair | N/A | — |
| Fishbrain | Alexandrebodeart / 17204177 | Name: Alexandrey Bodeart Location: United States |
| Shodan | N/A | — |
| Untappd | Alexandrebodeart / 10895932 | Name: Alexandre Bodear Registered: 18 Aug 2023 |
| Nvidia | N/A | — |
| PayPal | N/A | Phone hint: +336 *** 3706 (France) |
| Foursquare | alexandb4444509 / 1399427273 | Name: Alexandrea Bodeart Location: Mulhouse, France |
This pattern of display names—including Alexandre Bodear, Alexandrey Bodeart, and Alexandrea Bodeart—suggests possible use of variants or typographical mutations of the same identity across platforms. The repeated geolocation references to Mulhouse, France, reinforce the probable real-world connection.
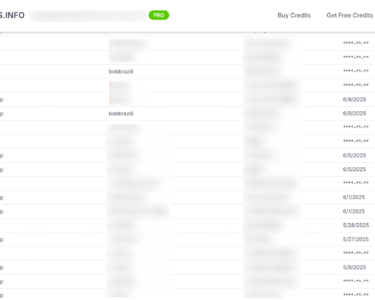
Exposure in Breach Datasets
Further breach data analysis confirmed that the email tumetrouvesbeauoupas@gmail.com appears in multiple exposed datasets:
| Platform | Username / ID | Notes |
| Sphero | 2361725 | Member since: Sept 2023 Name: Alexandre Bodeart |
| Pandabuy | Transfer5 / 369855004 | No additional metadata available |
A related breach search for the name “Alexandre Bodear” within Pandabuy’s dataset uncovered two phone numbers and a physical address located in Los Angeles, California (ZIP: 90001).
Additional searching for the same name with the geographic keyword “France” yielded a match on AllTrails.com:
- User ID: 67672297
- Location: Mulhouse, Haut-Rhin, France
Conclusion: Mapping a Threat Actor Through OSINT and Breach Intelligence
The case of Sanggiero illustrates how a fragmented digital footprint—when examined through the lens of structured OSINT and breach data—can reveal critical insights into a threat actor’s identity, behavior, and infrastructure.
Leveraging Flare, we were able to trace forum activity, Telegram channel, and associated cryptocurrency footprints tied to Sanggiero, including promotional content for stolen data and tools linked to real-world cyberattacks such as the breach of Acuity Inc, allegedly coordinated with IntelBroker.
Using Web.archive.org, we preserved and analyzed historical content from sanggiero.com, uncovering cryptocurrency donation addresses and blog posts openly describing unauthorized access to systems, data theft, and attack methods.
With Osint.industries, Epieos, osint.lolarchiver.com, we correlated the email address tumetrouvesbeauoupas@gmail.com with multiple platforms and aliases.
Through breach data analysis, we identified leaked records associated with this email, confirming registration on platforms like Breachforums, Sphero, Pandabuy.
These findings highlight the importance of combining multiple layers of investigation:
- Flare for historical threat actor monitoring and dark web telemetry
- archive.org for retrieving archived snapshots of website content and infrastructure
- Osint.industries, Epieos, osint.lolarchiver.com for email pivoting and/or username enumeration
- Breach data correlation for identity enrichment and attribution
Taken together, these tools form a powerful arsenal for investigators, enabling the reconstruction of complex identities behind aliases like Sanggiero. While direct attribution must be handled with caution, the convergence of indicators—IPs, aliases, domains, posts, emails, and crypto trails—strengthens the intelligence picture and supports further operational or legal action.
A visual representation of Sanggiero’s key connections is illustrated below through a Maltego graph