Introduction
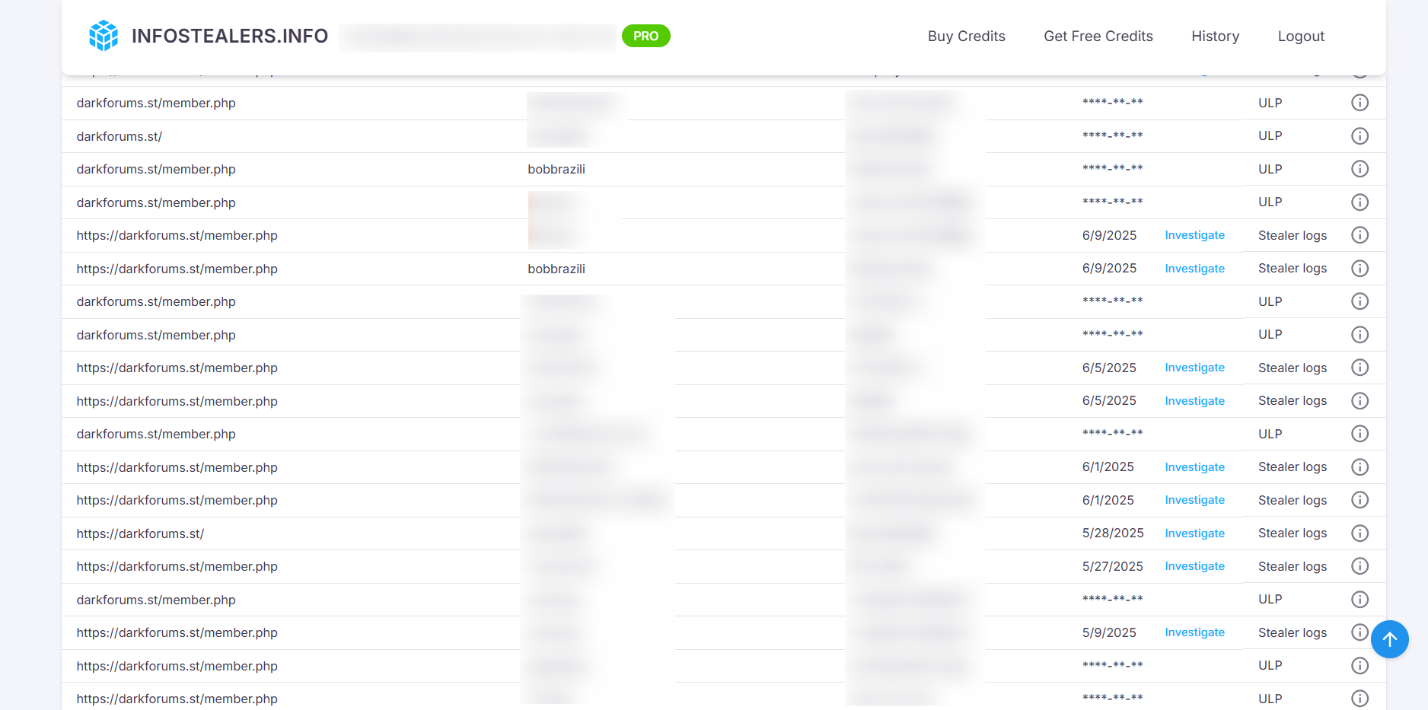
In May 2025, we introduced how Infostealers.info enables ethical investigators to potentially deanonymize and track threat actors operating on deep and dark web forums. In a previous investigation, we exposed a vendor active on BreachForums. Following that platform’s disruption, many vendors migrated to alternative cybercrime hubs—one of them being DarkForums[.]st.
Infostealers.info – Monitoring & Detection

During our monitoring, we identified a vendor operating under the alias “bobbrazili”, registered on DarkForums[.]st and involved in selling the following datasets:
- 1TB ULP leak – 16 billion records in 30 txt files (2024–2025), posted 28 June 2025
- 16 billion latest data leak (2024–2025) – reposted 30 June 2025
- 1.2M Binance leads & 272K Ledger customer records – posted 1 July 2025
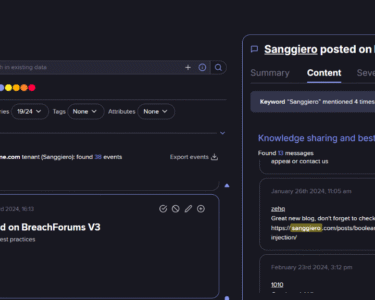
Infostealers.info – Cross-Platform Attribution & Profiling

- Compromised DarkForums password also linked to accounts on 14 other platforms including GitHub, faucetpay.io, satoshioffers.com, and rdphostings.com
- Use of 4 unique email addresses and 4 unique usernames across the above 14 platforms
- Accounts compromised on Binance, Coinbase, PayPal, Skrill, Coinpayu
- Presence on leakbase[.]io and hackerone[.]com via compromised records
- 1 CPF number used across 38 unique login paths
- 56 logins on .com.br domains
- 124 password records containing a first name strongly indicating identity
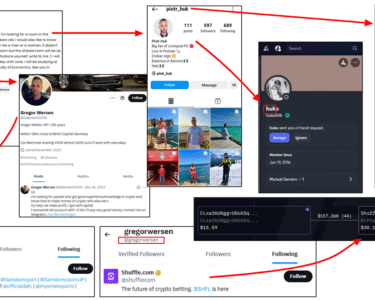
- 141 login records revealing the first name and 7 unique email addresses—when correlated, these records disclose the individual’s full name
- A Brazilian phone number linked to 4 login records
Beyond the Investigation – The Strategic Power of Infostealers.info
Rather than simply concluding, this case underscores how Infostealers.info acts as a force multiplier for threat intelligence operations.
- Real-Time Monitoring: Continuous tracking of compromised data across forums ensures investigators can act as soon as new threats surface.
- Attribution Capabilities: By correlating usernames, IPs, and leaked credentials, investigators can connect activities across multiple platforms and uncover real-world identities.
- Profiling Depth: Cross-referencing disparate leaks can reveal patterns such as geographic origin, linked financial accounts, and even personally identifiable information.
- Historical Context: Access to legacy breach data enables profiling over time, showing how a threat actor’s tactics, data sets, and platforms evolve.
In this investigation, the ability to pivot from a single username to a detailed digital footprint—spanning platforms, leaks, and geographies—demonstrates the tangible advantage of integrated monitoring, attribution, and profiling. For security teams, journalists, and researchers, Infostealers.info is not just a data source—it is an intelligence engine.