What Are Crypto Drainers?
Crypto drainers are malicious toolkits designed to steal digital assets such as ETH, SOL, USDT, NFTs, and other tokens. They typically operate by tricking users into signing fraudulent transactions via phishing websites, fake dApps, or compromised platforms. These campaigns often impersonate legitimate services or exploit user trust through social engineering.
Drainers target widely used wallets, including Phantom, Solflare, WalletConnect, Tronlink, OKX Wallet, Ledger, Coinbase Wallet, and BitGet. They’re engineered for maximum extraction, prioritizing high-value assets like ETH, and USDT.
Behind the scenes, drainer kits are distributed through cybercrime channels—primarily Telegram groups or channels, and darknet forums, sold for prices ranging between $500 and $10,000. This includes access to source code, admin panels, exploit libraries, or full Drainer-as-a-Service (DaaS) subscriptions.
Why This Research Matters
Crypto drainers remain a blind spot for much of the cybersecurity and blockchain security community. As a fast-evolving subcategory of the cybercrime-as-a-service economy, they warrant deeper scrutiny from both investigators and platform defenders.
This research aims to fill that gap by mapping active crypto drainer infrastructure and identifying dominant drainer kits based on web-based signals.
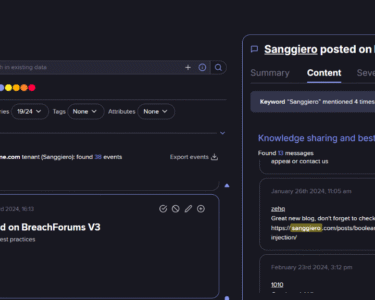
Tracking Drainer Infrastructure with SilentPush
Using SilentPush, we analyzed the landscape of crypto drainer websites observed from January to July 2025.
- 122 crypto drainer domains were identified.
- 54 domains remained active at the time of analysis.
- The remaining 68 were inactive, possibly taken down or abandoned.
Many of these domains used keywords such as “Drainer”, “Web3”, “NFT”, “TON”, or “Solana” in their HTML titles. Others used misleading names like airdrop2025[.]monster or dailydebtdrainer[.]com to entice victims with fake airdrops or reward programs.
Most prevalent drainer clusters (based on HTML title and number of domains/servers):
| HTML Title | Domains / Servers |
| Ton Drainer – Demo Page | 12 |
| Tron Drainer | 12 |
| EVM Drainer | 4 |
| Inferno Drainer | 4 |
| Miller Drainer | 3 |
| MS Drainer | 3 |
| Golden Drainer | 3 |
| Crypto Drainers Premium | 2 |
| TA505 (Evil Corp) Drainer | 2 |
| A.D.S. MULTICHAIN DRAINER by KORTE | 2 |
| CozartWeb | Test Drainer | 2 |
| Quark Drainer (480+ Wallets) | 2 |
| Others (Ace, Fusion, Hexly, etc.) | 2 each |
Notably, 18 out of the 54 active sites were linked to Telegram accounts, which likely serve as drainer support hubs, and sales outlets.
Hosting & Infrastructure Insights
The 54 active domains were hosted across 9 countries, with some obfuscated via Cloudflare, masking their true origin IPs.

| Provider | Jurisdiction (Legal Registration) | IP Count |
| Cloudflare Inc | United States | 15 |
| Amazon Technologies | United States | 6 |
| Hostinger International | Cyprus | 4 |
| Hypercore Ltd | Israel | 2 |
| Aeza Group / Intl | Russia / UK | 2 |
| Advania Island ehf | Iceland | 1 |
| Green Floid LLC | United States | 1 |
| Akamai Connected Cloud | United States | 1 |
| Beget LLC | Russia | 1 |
| Hostinux Limited | United Kingdom | 1 |
| PONYNET | Canada | 1 |
| TIER-NET | United States | 1 |
| YottaSrc | Romania / Saudi Arabia | 1 |
| Global Internet Solutions LLC | United States | 1 |
| Global-Data System IT Corporation | United States | 1 |
| Namecheap | United States | 1 |
Some drainers rely on CDNs and cloud platforms that don’t actively screen for phishing content, enabling continued abuse of their infrastructure.
Domain TLD Patterns
The chart below shows the distribution of active crypto drainer domains by top-level domain (TLD).

For Crypto Users:
- Avoid unsolicited links, especially airdrop or giveaway claims.
- Verify transaction prompts and wallet connection requests.
- Use hardware wallets and enable 2FA where possible.
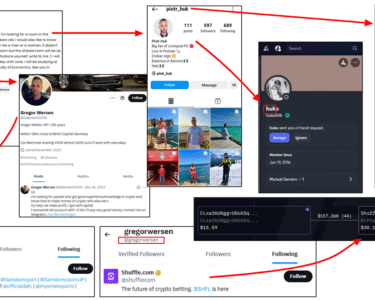
For Investigators:
- Monitor Telegram and dark net forums for drainer sales and deployment.
- Analyze newly registered domains referencing “drainer”, “TON”, or similar terms.
- Partner with blockchain analytics firms (e.g., AMLBot) to trace funds and attribution.
For Platforms:
- Hosting/CDN providers (e.g., Netlify, Vercel, Cloudflare) must improve detection of phishing and scam websites.
- Social media platforms (especially X.com) should strengthen account security to prevent hijacked accounts being used for drainer promotion.