The Scale and Severity of Cyber Attacks Hitting UK Businesses
UK businesses are under growing cyber pressure. In 2024 alone, over 7.7 million attacks were recorded, with phishing, indirect breaches, and ransomware leading the charge. According to the Cyber Security Breaches Survey 2025, 43% of UK businesses and 30% of UK charities experienced at least one cyber breach or attack in the 12 months prior to April 2025—translating to approximately 612,000 businesses and 61,000 charities.
Of these, around 20% were confirmed victims of actual cybercrime. While ransomware accounted for only 1% (~19,000 businesses), the impact was severe. Public ransomware disclosures surged in Q2 2025 with 276 incidents, a 63% YoY increase. The healthcare (52), government (45), and services (33) sectors were hardest hit.
Notable attacks—such as those affecting M&S, Co-op, and logistics firm KNP—highlighted operational and financial risks. Despite the abundant NCSC guidance, only ~35,000 Cyber Essentials certifications have been issued across 5.5 million UK businesses, leaving a vast majority exposed.
Case in Point: KNP Logistics and the Cost of One Weak Password
In June 2025, a ransomware attack by the Akira group brought down KNP Logistics, a 158-year-old transport firm. Hackers accessed critical infrastructure after guessing a weak employee password, encrypted key systems, and demanded a ransom up to £5 million. Despite having cyber insurance, the firm couldn’t recover—leading to its collapse and the loss of ~700 jobs. This stark example underscores the ripple effects of compromised credentials.
Infostealer Infections: A Silent, Widespread Threat
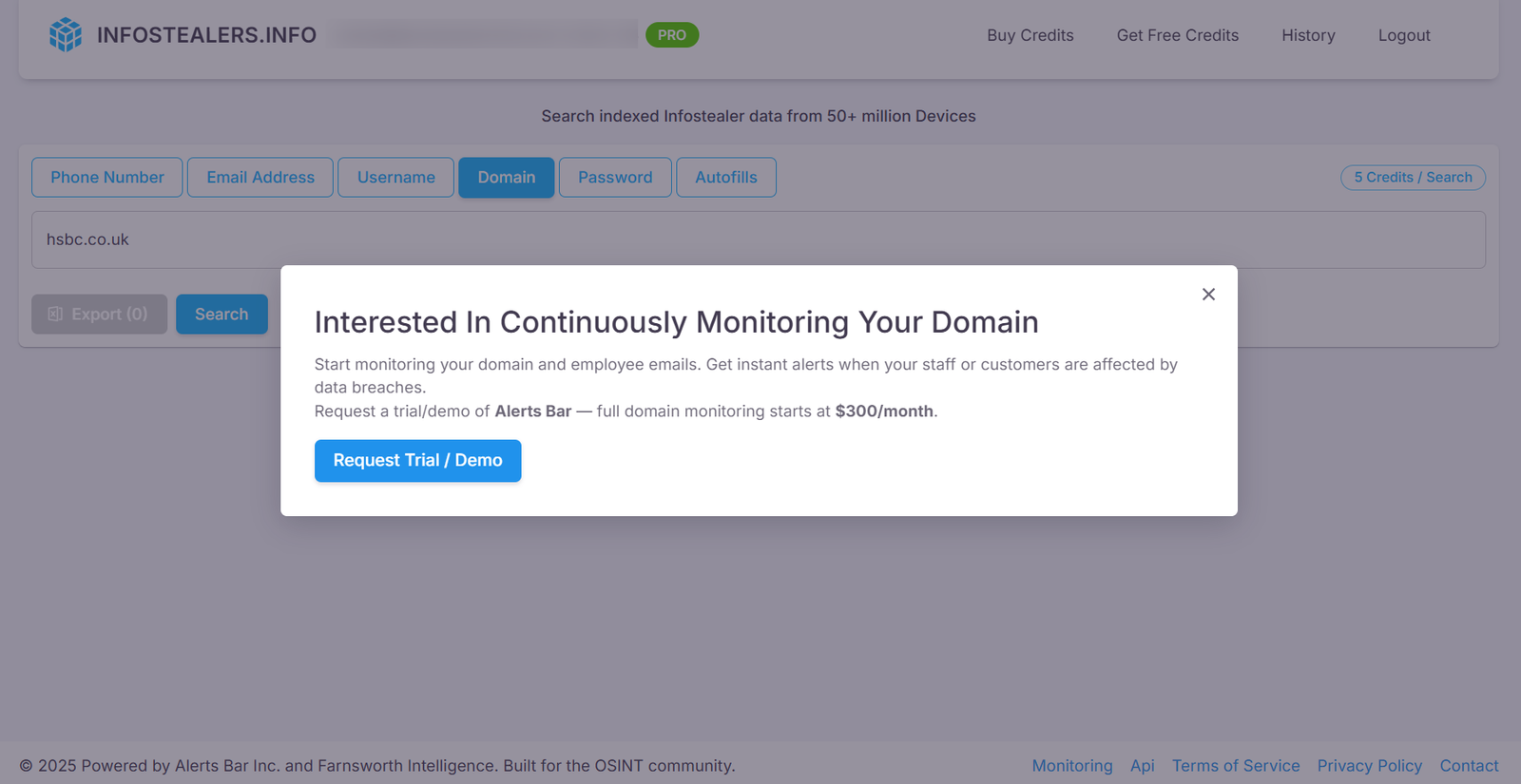
While ransomware grabs headlines, infostealer malware operates quietly—harvesting credentials, browser data, and authentication tokens to fuel future breaches. According to data from Infostealers.info, over 123,000 infostealer infections were recorded in the UK by July 2025 (excluding ULP logs), with infections rising steadily month-on-month.
These infections affect organizations of all sizes, from enterprise giants to small and micro firms. Our research leveraged Infostealers.info to profile the exposure across the UK market, segmented by company size and sector. The findings make a compelling case for integrating infostealer monitoring into proactive defense strategies.
Sector-by-Sector Impact in 2025
| Sector | Notable Incidents |
| Healthcare | 52 ransomware cases (Q2 2025) |
| Government & Public | 45 ransomware cases |
| Services | 33 attacks (professional and technical) |
| Retail | M&S and Co-op breaches; projected £300M loss for M&S |
| Construction, Hospitality, Arts | Elevated ransomware rates |
Breach Exposure by Business Size
- Large enterprises: 74% reported breaches; ~14% suffered ransomware attacks.
- Medium enterprises: 67% reported at least one incident.
- Small/micro businesses: Lower reported rates, but likely underreported.
Infostealer Exposure Among Top Public Companies (By Revenue)
| Company | Sector | Website | Total Compromises | ULP Logs | Infostealer Logs |
| Tesco | Retail | tesco.com | 68,376 | 55,257 | 13,119 |
| Vodafone | Telecommunications | vodafone.com | 64,257 | 52,094 | 12,163 |
| Shell | Oil & Gas / Energy | shell.com | 47,852 | 39,483 | 8,369 |
| HSBC | Banking | hsbc.co.uk | 14,402 | 12,585 | 1,817 |
| BP | Oil & Gas / Energy | bp.com | 12,417 | 9,619 | 2,798 |
| Unilever | Consumer Goods | unilever.com | 9,162 | 7,768 | 1,394 |
| Barclays | Banking | barclays.co.uk | 6,345 | 5,321 | 1,024 |
| AstraZeneca | Pharma | astrazeneca.com | 1,250 | 1,038 | 212 |
| Lloyds | Banking | lloydsbank.com | 873 | 769 | 104 |
| Rio Tinto | Mining | riotinto.com | 794 | 632 | 162 |
Case Study: Unilever
- 9,000+ Compromises (February 2022–July 2025)
- 2,300+ @unilever.com emails compromised (417 infostealer logs)
- Top URL paths compromised: idp.unilever[.]com/adfs, ul-amigopod-e.unilever[.]com, web3.inpartner[.]unilever.com, uflp.unilever[.]com/tgwebhost
- ~42% reused passwords, ~60% patterned passwords
*Note: Patterned passwords refer to those following easily predictable structures, such as sequential numbers, company-related terms, dates, or simple keyboard patterns (e.g., “123456” or “qwerty”).
Privately-Owned Companies by Turnover: Infostealer Exposure
| Company | Sector | Website | Compromises | ULP Logs | Stealer Logs |
| Wise | Fintech payments | wise.com | 138,932 | 84,898 | 54,034 |
| MoneySuperMarket | Personal finance platform | moneysupermarket.com | 39,159 | 33,667 | 5,492 |
| M&S Supply Chain | Retail logistics | marksandspencer.com | 17,075 | 14,171 | 2,904 |
| Auto Trader | Digital automotive marketplace | autotrader.co.uk | 13,583 | 11,779 | 1,804 |
| Pets at Home | Retail pet care services | petsathome.com | 4,854 | 3,948 | 906 |
Case Study: M&S Supply Chain
- 17,000+ Compromises (February 2022–August 2025)
- Two confirmed employee email compromises (1 associated with an infostealer log; 1 with a ULP log)
- Most affected mail providers: Gmail (5,889), Hotmail (1,415), Yahoo (656)
- Frequently targeted login paths included: “MSResUserRegistration”, “MSResLogin”, “MSCheckoutLoginFormCmd”
- ~57% reused passwords, 11% patterned
*Note: Patterned passwords refer to those following easily predictable structures, such as sequential numbers, company-related terms, dates, or simple keyboard patterns (e.g., “123456” or “qwerty”).
Small & Micro Business Compromises
| Company | Sector | Website | Compromises | ULP | Stealer Logs |
| Simmer Eats | Meal subscriptions | simmereats.com | 123 | 70 | 53 |
| Montirex | Apparel | montirex.com | 27 | 20 | 7 |
| Healf | Health retail | healf.com | 12 | 7 | 5 |
| Dfyne | Activewear | dfyne.com | 6 | 4 | 2 |
| Odd Muse | Fashion | oddmuse.co.uk | 5 | 4 | 1 |
Case Study: Simmer Eats
- 123 infections, 44 in 2025 alone
- Top affected mail domains: Gmail (83), Hotmail (11), Outlook (10)
- Top compromises by URL Path: simmereats[.]com/login (55), simmereats[.]com/join-now/account (41)
- 65 unique passwords: 90% strong, yet 47% patterned
Conclusion: Why Infostealer Monitoring Must Be Central to Cyber Strategy
Infostealer malware represents a silent yet potent threat across every level of the UK economy. From Fortune 100 multinationals to thriving microenterprises, compromised credentials are now a common entry point for ransomware, fraud, and long-term infiltration.
Despite rising awareness of cyber threats, many UK businesses remain underprepared—especially across their supply chains, which often act as soft entry points for attackers. The cases of KNP Logistics, and Unilever, show how just a handful of compromised credentials can cascade into catastrophic disruptions.
Infostealer monitoring, credential hygiene, and real-time threat intelligence must now be integrated into the core of UK organizations’ cyber defence frameworks—not only to mitigate present-day vulnerabilities, but to build resilience against tomorrow’s compromises.
Proactive defence is not a luxury—it’s a business continuity imperative.