Introduction
Phishing kits and panels targeting cryptocurrency exchanges—particularly Coinbase— are evolving rapidly, with threat actors focusing on social engineering techniques aimed directly at customers. Data from Infostealers.info reveals over 150,000 recorded infections, underscoring a vast pool of compromised data that bad actors can exploit to identify and deceive Coinbase users.
These operations frequently begin with the analysis of logs harvested from infostealers, combined with other forms of leaked personal information, which are used to tailor phishing lures and scam communications. Telegram appears to be the primary coordination platform for these activities, serving as a hub where actors trade phishing panels, logs, wallet-draining tools, and methods for bypassing security measures.
Our ongoing monitoring of Telegram groups and channels reveals a growing trend: the proliferation of phishing panels and social engineering playbooks specifically designed to compromise Coinbase accounts. These campaigns are often discussed openly and are dominated by a younger demographic—predominantly teenagers—motivated by the promise of fast financial gains. Based on linguistic cues, timestamps, and recurring geolocation indicators in their conversations, we assess that many of these young individuals are based in the United States.
However, the development of the phishing panels themselves frequently originates from groups or individuals based abroad, particularly in countries like Russia or China. These panels are not always used by their creators directly; instead, they are often rented out or sold as part of a phishing-as-a-service (PhaaS) model. In this ecosystem, the developers provide ready-to-deploy phishing kits in exchange for a commission or fixed fee, enabling less technical users to launch scams with minimal setup.
In this article, we have investigated one such phishing toolkit specifically engineered to target Coinbase users. We have explored its features, distribution methods, operational playbook, and the Telegram-based infrastructure that facilitates its deployment—offering a comprehensive overview of the expanding phishing-as-a-service model aimed at crypto platforms.
Plague Panel: Fast-Deploy Phishing for Coinbase Drains
Plague Panel (“007 Panel” affiliate), identified as a Telegram channel (ID: 2673101059; 2,886 subscribers), was set up on 7 May 2025. It provides Coinbase-focused malicious control panels with bi-weekly and monthly subscription plans, as detailed in the accompanying screenshot. Plague Panel is a dashboard used by cybercriminals to coordinate phishing and data theft operations. It functions as a centralized hub for managing attacks, including deploying phishing pages, collecting stolen credentials, and automating social engineering tasks. During the week of 18–24 May 2025, the cybercriminal group operating Plague Panel reportedly claimed to have stolen $30,000 USD from Coinbase users.


Plaguedev (ID: 7843119517) also serves as the administrator of “Plague Redirect” (ID: 2644261077; created 7 May 2025; 552 subscribers; t.me/plagueredirect), which lists:
- Dev Service: @plaguetools (ID: 2129053393; created on 27 December 2023; 915 subscribers; latest post 7 May 2025), offering services such as Coinbase tools (private panels, “autodoxxers”, EVM Drainer, and custom requests). Contact: @plaguedev
- Coinbase Panel: @plaguepanel (ID: 2673101059).
- Plague Vouches: @plaguevouches1 (ID: 2540324856; 124 members), a chat for user endorsements of their services, where user @traitor (ID: 7535054004) was listed.
Plaguedev (ID: 7843119517) has been linked to several historical usernames and display names on Telegram, as detailed below.
| Telegram Username | Date | Telegram Display Name | Date |
| plaguedev | 8 May 2025 | Plague Suрроrt | 8 May 2025 |
| hi82874 | 7 May 2025 | kh | 7 May 2025 |
| khanasadi | 6 April 2025 | lebon bоn | 6 April 2025 |
| lebrondev | N/A | N/A | N/A |
The following Telegram groups were identified as being associated with Plaguedev (ID: 7843119517).
| Telegram group / Link | Notable Details |
| OFM Goats | Jobs & Hirings (t.me/OFMCareers) | 3 messages |
| OFM Jobs, Hiring, Vas (t.me/ofmjobs) | 4 messages |
| OFM Jobs and VA’s |MESH| (t.me/OFMjobsandhiring) | 3 messages |
| Albanian Drainer Chat (t.me/albaniandrainerchat) | 3 messages |
| OLD RRC СHAT (t.me/c/1151669222) | 3 messages |
| dеgen chаt (t.me/c/1892655110) | 3 messages |
| Skidмark v3 (t.me/c/2289759615/) | 1 message |
On 6 May 2025, @Plaguedev (ID: 7843119517) shared a message in the Albanian Drainer Chat (@albaniandrainerchat), promoting another Telegram channel, @zeyrodev (ID: 2671227399). A screenshot of the message is included below.

| Telegram channel | Notable Details |
| Albanian Drainer (t.me/albaniandrainer) | 3 messages |
| Rolls Rоуcе Сashouts (t.me/rollsroycecashoutsagain) | 3 messages Inactive channel |
Further analysis of the Telegram user @traitor (ID: 7535054004; premium account) has uncovered connections to Plague Panel. The historical Telegram usernames and display names associated with this user are presented in the table below.
| Telegram Username | Date | Telegram Display Name | Date |
| traitor | 19 May 2025 | traitor | 22 May 2025 |
| legalwork3 | 10 May 2025 | t | 22 May 2025 |
| lumiras | 3 May 2025 | brеtt | 19 May 2025 |
| liolumi | 26 April 2025 | х | 16 May 2025 |
| chiseltipjosh | 11 April 2025 | Luмirа | 8 May 2025 |
| lumiraaa | 8 April 2025 | riсh ass nigga | 2 May 2025 |
| MiIadyno20 | 7 April 2025 | lumi | 27 April 2025 |
| feelingevil | 1 February 2025 | josh | 26 April 2025 |
| jacksofm | 29 January 2025 | Miladу no. 20 | 8 April 2025 |
| coolzebra | 7 January 2025 | kh | 7 April 2025 |
| Knownkid | 22 December 2024 | khalid | 4 April 2025 |
| Sleepyheepy | 20 December 2024 | fаntasу | 31 March 2025 |
| N/A | N/A | nonchаlant | 29 March 2025 |
| N/A | N/A | еvil | 15 March 2025 |
| N/A | N/A | nightfаll | 4 February 2025 |
| N/A | N/A | соolzebrа | 29 January 2025 |
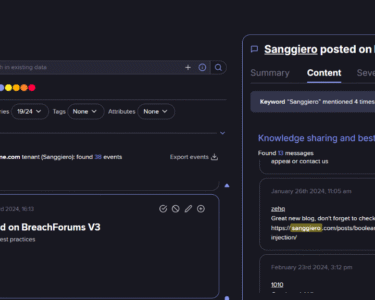
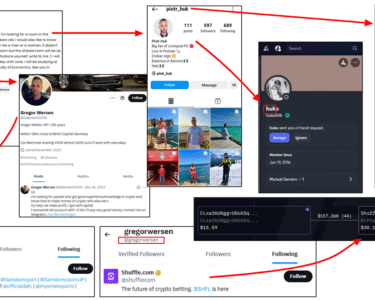
The historical usernames strongly suggest that @Plaguedev (ID: 7843119517) and @traitor (ID: 7535054004) are highly likely the same individual. Using StealthMole, we analyzed the historical profile images and Telegram activity linked to @traitor (ID: 7535054004). A screenshot provided below captures past activity under the @sleepyheepy username, where the user was involved in offering Google ads services. Additionally, one of their profile photos revealed Solana transactions.


On 23 May 2025, the admin @feelingevil posted about Plague Development. A separate Telegram channel, @lumiraaa (ID: 2491123931; created 11 April 2025; 6 subscribers), associated with @traitor (ID: 7535054004), was found promoting Plague Panel. Additionally, @traitor (ID: 7535054004) was observed advertising Plague Panel in the wizard chat (@drainergroupchat). On 15 February 2025, @traitor (ID: 7535054004) was identified as seeking to hire a virtual assistant in the Telegram chat OFM Jobs and VA’s |MESH| (@OFMjobsandhiring). A screenshot is provided below.




The username @Iniggas is associated with a Telegram channel named “Lisenced” (ID: 2348546674; 5 subscribers), where certain users endorse @Iniggas’ services, including the sale of an autodoxxer and Solana exchanges. A screenshot is included below. Notably, a user named “PrimaxOG” (@undergroundflex; ID: 6546576330) was found vouching for @Iniggas’ services.

| Telegram group / Link | Notable Details |
| OFM Jobs and VA’s |MESH| (t.me/OFMjobsandhiring) | 23 messages |
| Star Fraud chat (t.me/Starfraudgc) | 15 messages |
| Telegram Developers Community (t.me/devs) | 27 messages |
| Star chat (t.me/starfraudgroupchat) | 28 messages |
| Escrow Vouches (t.me/portfolio) | 1 message |
| wd chat (t.me/wdgroupchat) | 30 messages |
| OGU Chat (t.me/chatter) | 1 message |
| wizard chat (t.me/drainergroupchat) | 46 messages |
| ##TTM Chat (t.me/ttmcashoutschat) | 8 messages |
| Jobledger – Crypto & Web3 Jobs Hiring 👽🧳🚀 (t.me/jobledger_hirings) | 1 message |
| Blockvizr Marketplace (t.me/Blockvizr_Marketplace) | 4 messages |
| Вlockvizr Info (t.me/Blockvizr) | 9 messages |
| [chat] (t.me/draingc) | 3 messages |
| SNP500 (t.me/snp500pal) | 1 message |
| Skidmаrk v3 (t.me/c/2289759615) | 8 messages |
| Mоnster. (t.me/c/2560362156) | 11 messages |
| Spazzing (t.me/spazzing) | 2 messages |
| Crypt Service | Услуги Крипта (t.me/cryptservice) | 9 messages |
| Inferno Drainer FAN Community (t.me/infernodrainercommunity) | 2 messages |
| cаtboу bо$$ chаt (t.me/yapcentral) | 4 messages Suspended by Telegram |
| Chest Chat (t.me/chest) | 2 messages |
| ETHHEAT CHAT (t.me/ethheatchat) | 1 message |
| Albanian Drainer Chat (t.me/albaniandrainerchat) | 1 message @feelingevil; @traitor; @plaguedev; @lebronmailer are listed and linked together in this group |
| Peaсeful Grouрс (https://t.me/c/1056750818) | 169 messages |
| OFM – Jobs, Hiring, Vas (t.me/whalesofmjobs) | 18 messages
|
| OFM Jobs, Hiring, Vas (t.me/ofmjobs) | 14 messages
|
| OFM Goats | Jobs & Hirings (t.me/OFMCareers) | 14 messages |
| меow Chat (t.me/c/2058892638/) | 12 messages |
| Сoinbаsе НQ (t.me/c/2411363077) | 15 messages |
| Drаinеrs (t.me/c/2365712700) | 9 messages |
| Com Chat (t.me/comchat) | 2 messages |
| dеgen chat (t.me/c/1892655110) | No messages |
Intelligence Analysis of Telegram Chat Data Linked to @traitor (ID: 7535054004)
An analysis of Telegram chat messages from multiple groups and channels has been conducted to profile and identify behavioral patterns associated with @traitor (ID: 7535054004). A summary of the findings is presented below.
- Repeat Usernames
The following usernames appear multiple times across different groups:
- @feelingevil: Appears frequently (over 30 instances) across multiple groups, including @drainergroupchat, @ttmcashoutschat, @Blockvizr, @yapcentral, @spazzing, @Peaceful Groupchat, and others. This user is heavily involved in seeking high-quality (HQ) data, SMTPs, Twitter accounts, and advertising methods. They also express interest in memecoins, draining, and buying tools.
- @lockindude: Appears multiple times (at least 10 instances) in @Peaceful Groupchat and Star chat, associated with promoting an EVM drainer with bypass capabilities.
- @superkitty27: Appears in multiple identical posts (over 10 instances) in @starfraudgroupchat, seeking HQ data providers with specific requirements (doxxed, verified, 5-7 figure potential).
- @lumiraaa: Appears in @draingc, @Blockvizr, and @wdgroupchat, seeking Twitter Blue providers and involved in Twitter takeovers or social engineering (SE) operations.
- @chiseltipjosh: Appears in @drainergroupchat, @ttmcashoutschat, and @Blockvizr_Marketplace, requesting website cloning services for fraudulent purposes.
- @drainmethods: Appears in @drainergroupchat, @ttmcashoutschat, and Monster chat, promoting drainer methods, indicating involvement in crypto drainer schemes.
- @lebronmailer: Appears in @ethheatchat and @infernodrainercommunity, promoted as the “best mailer”, likely involved in email spoofing or phishing campaigns.
These usernames suggest a network of individuals or aliases engaged in coordinated fraudulent activities, including data acquisition, crypto draining, and social engineering.
- Technical Projects Related to Coinbase
Several messages reference Coinbase explicitly, often in the context of fraudulent activities. Below are the key projects and details:
- Coinbase Data Acquisition:
- 12 Feb 2025, @Peaceful Groupchat: A user asks, “How do ppl get cb data?” and “hack cb?” indicating interest in stealing Coinbase user data.
- 24 Feb 2025, @devs: A user seeks Coinbase HTML email templates that avoid spam filters, likely for phishing campaigns targeting Coinbase users.
- 21 Mar 2025, @rollsroycecashoutsgroupchat: @feelingevil seeks an “autodoxxer and coinbase vm”, suggesting a targeted approach to exploit Coinbase accounts.
- Coinbase Phishing and Draining:
- 24 Feb 2025, @Peaceful Groupchat: A user asks if “@support-coinbase.com” is a good domain, likely for spoofing Coinbase support emails in phishing attacks.
- 4 Mar 2025, @Peaceful Groupchat: @feelingevil mentions “pay.coinbase” in a post seeking HQ data providers, possibly referring to a Coinbase-related payment method or scam.
- Coinbase HQ Chat (ID: 2411363077; 327 members):
- 10 Jan 2025, @Coinbase HQ: Multiple posts offer quick tasks for $25-$50, including requests for “draining chats” and questions about Google and malware (e.g., “Bro is the ipa shi malware”). This chat appears to be a hub for Coinbase-related fraud discussions.
These activities suggest a focus on phishing, data theft, and social engineering to compromise Coinbase accounts, likely using fake domains, email templates, and drainers.
- Links to Crypto Drainers
The chat data references several crypto drainers, which are malicious tools designed to steal cryptocurrency from victims’ wallets. Key drainers and related details:
- Albanian Drainer:
- 21 Mar 2025, @albaniandrainerchat: @feelingevil seeks UHQ data providers, claiming potential for 6-figure earnings.
- Inferno Drainer:
- 21 Mar 2025, @infernodrainercommunity: @lebronmailer is promoted, and earlier posts seek HQ data.
- EVM Drainer by @lockindude:
- 17 Feb 2025, @Peaceful Groupchat, Star chat: @lockindude is repeatedly promoted for an “EVM drainer w bypass” (Ethereum Virtual Machine drainer), targeting ERC20 tokens. The user seeks “experienced shawts only”.
- 19 Feb 2025, @Peaceful Groupchat, Star chat: Multiple posts advertise @lockindude’s drainer, with claims of bypassing security measures.
- Targets
The chat data indicates several targets for fraudulent activities:
- Coinbase Users:
- Explicit mentions of Coinbase data, and phishing templates suggest Coinbase account holders are a primary target for data theft and account takeovers.
- Example: 24 Feb 2025, @PeacefulGroupchat, seeking Coinbase HTMLs and spoofed domains.
- Crypto Wallet Holders:
- Drainers like @lockindude’s ETH drainer and Inferno Drainer target users holding ERC20 tokens or other cryptocurrencies, likely through phishing or fake dApps.
- Example: 5 Feb 2025, @Blockvizr_Marketplace, selling an ETH drainer for ERC20 tokens.
- Social Media Users:
- Twitter Blue and verified Twitter accounts are sought (e.g., 19 Mar 2025, @ttmcashoutschat; 8 Apr 2025, @Blockvizr), likely for impersonation or social engineering.
- Instagram, Reddit, and TikTok accounts with good followings are also targeted (27 Jan 2025, @OFMjobsandhiring).
- General Public:
- Posts seeking HQ/UHQ data (e.g., 23 Mar 2025, @ttmcashoutschat) and advertising methods (3 Apr 2025, @OFMjobsandhiring) suggest broad targeting of personal data for fraud.
- Memecoin enthusiasts are targeted (5 Apr 2025, @drainergroupchat), likely for pump-and-dump or drainer scams.
What Did the Plague Panel Investigation Uncover?
Our analysis of the Plague tool revealed that the user “Khalidibnwaleed” [Khalid Ibn Waleed] demonstrated a live screen preview of the tool’s structured interface, featuring a control panel with options such as “Send to Sign In”, “Send to Password Reset”, “Send to Transaction Cancellation”, and “Invalid Input”. The “Send to Sign In” function redirects users to a Coinbase-specific panel. The user showcased the following dummy Gmail addresses:
- scythediscordmm@gmail.com – associated with the now-inactive Discord server “Scythe MM Services” (scythemm)
- hmmm123@gmail.com
The email scythediscordmm@gmail.com was investigated across various platforms and services using Osint.industries. A summary table of the findings is presented below.
| Platform | Username / ID | Notable Details |
| 104827711096288784794 | Last Seen: 5/16/2025 11:04:19 PM | |
| KhanAcademy | Scythediscordmm / kaid_8811466340820990287833098 | N/A |
| Chess[.]com | SoupOnTop / 281641539 | Registered: 2 May 2023 Last Seen 5/19/2024 9:49:16 PM Geolocation: United States |
| Gravatar | Scythediscordmm | N/A |
| Adobe | N/A | Authentication provider: Google |
| Bandlab | user8462437754625597 | Registered: 17 March 2024 Name: Scythe |
| PayPal | N/A | Phone Number Hints: +19 *** 5656 Cards Hint: Visa |
| X.com | N/A | Phone Number Hints: +19 *** 5656 |
| Microsoft | EB2C721C04581040 | Name: Scythe MM Geolocation: United States |
| Kwork (Russian platform) | N/A | N/A |
| Spotify | N/A | N/A |
| Fiverr | N/A | N/A |
| N/A | N/A |
Digging Deeper: Identification of Phishing Panels – Inside 007.移动
During our investigations, two Coinbase-related phishing sites were identified and analyzed:
- 929871-coinbase.com (registered on 25 May 2025 through NICENIC INTERNATIONAL GROUP CO., LIMITED; behind Cloudflare)
- 812230-coinbase.com (registered on 21 May 2025 through NICENIC INTERNATIONAL GROUP CO., LIMITED; behind Cloudflare)
The analysis of the source-code for 929871-coinbase.com uncovered the following three JavaScript files.
- js/screenCapture.js (html2canvas)
- Purpose: Captures screenshots of webpages by rendering DOM elements to a canvas.
- Functionality: Clones DOM, parses CSS, renders text, images, and effects (e.g., shadows, gradients). Supports CORS, proxies, and iframe cloning.
- Malicious Use: Used in phishing to capture user interactions (e.g., login forms, seed phrase inputs) on fake Coinbase pages, transmitting screenshots to attackers.
- Details: Minified, obfuscated, authored by “James Bond”, with a copyright notice for 2024. Integrates with Socket.IO for data exfiltration.
- js/socket.io.js – IO (Socket.IO v4.7.5)
- Purpose: Enables real-time, bidirectional communication between client and server using WebSocket, polling, or WebTransport.
- Functionality: Manages connections, encodes/decodes packets (text/binary), supports namespaces, and handles reconnection with exponential backoff.
- Malicious Use: Facilitates live data exfiltration (e.g., credentials, screenshots) and server-driven control in phishing attacks targeting Coinbase and wallets.
- Details: Minified, obfuscated, same author/license as js/screenCapture.js. Connects to suspicious domains (e.g., 007.xn--6frz82g).
- js/main.js – Coinbase Specific Phishing Script
- Purpose: Executes a phishing attack to steal Coinbase user data (credentials, seed phrases, 2FA codes, identity documents).
- Functionality: Displays fake Coinbase UI (login, 2FA, recovery, verification), captures inputs/screenshots, and sends data via Socket.IO. Uses eval for server-sent payloads.
- Malicious Use: Targets Coinbase users, exfiltrates sensitive data in real time, and mimics legitimate flows to deceive users.
- Details: Tailored for Coinbase, relies on js/screenCapture.js and js/socket.io.js. Connects to 007.xn--6frz82g, includes Google/Apple auth scripts for legitimacy.
The C2 subdomain: nothing.007.xn--6frz82g (Domain: 007.xn--6frz82g)
The C2 subdomain nothing.007.xn--6frz82g was found to be resolving to IP address
77.239.124.32 (geolocation: Saint Petersburg, Russia; Aeza Group LLC; AS 216246).
The IP address 77.239.124.32 was found to be hosting the below subdomains / domains.
| Subdomain / Domain | Date Resolved | Detections (VirusTotal) |
| 9283321-coinbase.com | 2025-05-23 | 3 / 94 |
| 38927-coinbase.com | 2025-05-17 | 3 / 94 |
| staging-nothing.007.xn--6frz82g | 2025-05-15 | 0 / 94 |
| 928377-coinbase.com | 2025-05-07 | 16 / 94 |
| 923743-coinbase.com | 2025-05-07 | 5 / 94 |
| 109283-coinbase.com | 2025-05-06 | 2 / 94 |
| 283763-coinbase.com | 2025-05-04 | 6 / 94 |
| 9472338-coinbase.com | 2025-05-02 | 8 / 94 |
| 172628-coinbase.com | 2025-04-29 | 10 / 94 |
| 234551-coinbase.com | 2025-04-14 | 10 / 94 |
| 928341-coinbase.com | 2025-04-09 | 4 / 94 |
| 293784-coinbase.com | 2025-04-06 | 8 / 94 |
| 394675-coinbase.com | 2025-04-02 | 3 / 94 |
| account-unchained.com | 2025-03-08 | 1 / 94 |
| nothing.007.xn--6frz82g | 2025-03-08 | 0 / 94 |
| 653445-coinbase.com | 2025-03-08 | 6 / 94 |
The SSL certificate for the IP server 77.239.124.32 has been issued for Subject: nothing.007.xn--6frz82g.
Additional analysis of historical IP addresses hosting nothing.007.xn--6frz82g revealed more Coinbase-related phishing sites. Below is a summary table of the historical IP addresses and their associated subdomains/domains.
| Subdomain / Domain | Date Resolved | IP Server | IP Geolocation / ISP |
| nothing.007.xn--6frz82g | 2025-02-04
| 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| test-2282.xyz | 2025-02-17 | 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 183937-coinbase.com | 2025-02-17
| 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 394347-coinbase.com | 2025-02-19
| 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 622172-coinbase.com | 2025-02-21
| 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| tets-232332.xyz | 2025-02-23 | 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| test-28978.xyz | 2025-02-23 | 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 721464-coinbase.com | 2025-02-25 | 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 831474-coinbase.com | 2025-02-25
| 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| authorize-coinbase.com | 2025-02-25
| 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 432164-coinbase.com | 2025-02-26
| 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 52819-coinbase.com | 2025-02-27 | 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 293874-coinbase.com | 2025-02-28 | 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 653445-coinbase.com | 2025-04-06 | 89.22.239.110 | Sweden, Aeza International Ltd (AS 210644) |
| 4649585-coinbase.com | 2024-12-26
| 212.113.102.150 | Sweden, Aeza International Ltd (AS 210644) |
| nothing.007.xn--6frz82g | 2024-12-23 | 212.113.102.150 | Sweden, Aeza International Ltd (AS 210644) |
| 4649586-coinbase.com | 2024-12-23 | 212.113.102.150 | Sweden, Aeza International Ltd (AS 210644) |
| 1639585-coinbase.com
| 2024-12-16
| 212.113.102.150 | Sweden, Aeza International Ltd (AS 210644) |
| staging-nothing.007.xn--6frz82g | 2024-08-19 | 212.113.101.66 | Sweden, Aeza International Ltd (AS 210644) |
| nothing.007.xn--6frz82g | 2024-08-03 | 212.113.101.66 | Sweden, Aeza International Ltd (AS 210644) |
Analysis of historical IP resolutions indicates that this Coinbase-targeted phishing campaign began in December 2024. The favicon hash associated with the C2 domain 007.xn--6frz82g is -1921192219. A search on Fofa.info revealed the following domains and servers using this favicon hash.
| Domain / Server | Notable Details |
| files-admin-kroll.com | IP: 172.67.179.130, Cloudflare Inc SSL Certificate CommonName: files-admin-kroll.com |
| 77.239.124.32 | Historic ASN: 6908 Historic ISP: Six Degrees Technology Group Limited, United Kingdom Location: https://007.xn--6frz82g/login Server: nginx/1.22.1 |
| 007.xn--6frz82g | Login | 007.移动 172.67.71.106, Cloudflare Inc |
| 212.113.101.66 | ASN: 63023 Location: https://007.xn--6frz82g/login Server: nginx/1.24.0 (Ubuntu) |
The subdomain nothing.007.xn--6frz82g was also identified to be associated with three further domains via urlscan.io.
| Domain | Notable Details |
| onchain-coinbase.com | Registered: 13 September 2024 Registrar: NICENIC INTERNATIONAL GROUP CO., LIMITED Historic IP: 212.113.101.66 (geolocation: Sweden; Aeza International LTD) |
| oauth2-twitter.com | Registered: 22 August 2024 Registrar: NICENIC INTERNATIONAL GROUP CO., LIMITED Historic IP: 212.113.101.66 (geolocation: Sweden; Aeza International LTD) |
| summer-coinbase.com | Registered: 19 August 2024 Registrar: NICENIC INTERNATIONAL GROUP CO., LIMITED Historic IP: 212.113.101.66 (geolocation: Sweden; Aeza International LTD) |
The C2 domain 007.xn--6frz82g (007.移动) was registered through Namecheap, Inc on 18 July 2024, and currently uses Cloudflare’s CDN services. The domain’s top-level domain (TLD) .移动 translates to “mobile” in Chinese. The source code of 007.xn--6frz82g (007.移动) includes the following metadata:
- content=”007 Panel“
- “og:description” content=”Steal a little and they throw you in jail Steal a lot and they make you king.”
On-Chain Investigations
During our investigation, we identified the Ethereum address linked to Plaguedev (ID: 7843119517), the developer of Plague Panel:
- 0x29FaFF757CBCA9F9b110648548bB673e7e72fdE5
This address, abbreviated as 73e7e72fdE5, was found to be funded by Fake_Phishing188250, as detailed below via etherscan.io:
- 0x000037bB05B2CeF17c6469f4BcDb198826Ce0000 – the contract creator of this address was identified as 0x854dda621785DCA278df9b298825f2Ec32578B76 (via etherscan.io), tagged as Fake_Phishing182232 (0x0000553F880fFA3728b290e04E819053A3590000) and associated with Inferno Drainer (inferno-drainer-4.eth).
The address 73e7e72fdE5 received multiple transactions from 19826Ce0000 (its contract creator, labeled as Receiver on Arkham.com). A screenshot from Arkham.com is provided below.
A tag for the Ethereum address 73e7e72fdE5 has been created on AMLBot.com, enabling investigators to analyze its attribution and cluster data, including connections to centralized cryptocurrency exchanges.

This article highlights the role of intelligence-led investigation in disrupting phishing-as-a-service ecosystems targeting cryptocurrency platforms like Coinbase. By correlating infostealer-derived logs, Telegram network activity, and blockchain transaction patterns, investigators can:
- Map actor infrastructure across social, financial, and technical vectors—including phishing panels, Telegram aliases, and wallet transactions.
- Profile threat actors using behavioral indicators, linguistic cues, and device-level metadata to trace activity back to specific individuals or activity clusters.
- Trace transaction pathways via blockchain analytics, connecting phishing proceeds to tagged on-chain entities and drainer services.
- Detect and preempt toolkits by monitoring early-stage advertisement and beta testing of phishing kits and “autodoxxers” in niche Telegram groups and channels.
- Enable attribution through cross-platform identity overlaps, username reuse, and connected OSINT artifacts (e.g., favicon hashes, DNS resolutions, JavaScript reuse and tool-specific script signatures).